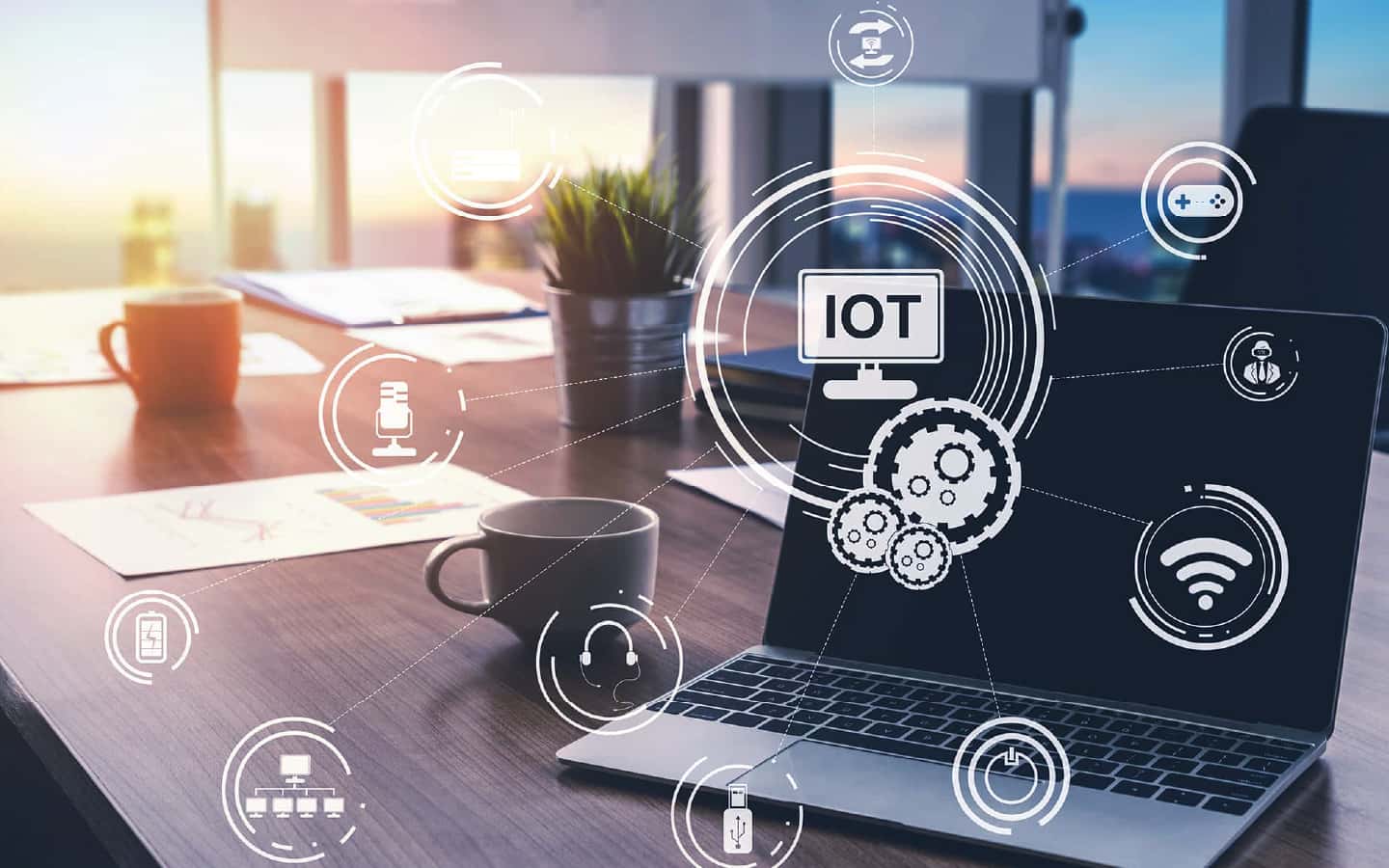
The third-party inspection operation is performed by an information security consultant and the inspection report is issued. The consultant team examines the information security requirements in different areas such as information systems, Internet of Things devices, application development, privacy and confidential data protection...etc. in accordance with international information security regulations and the various application technology standards and legal compliance requirements faced by the domestic promotion of innovative life applications.
Through the inspection operation, enterprises can understand the compliance with the information security requirements, and when there are items that do not comply with the team to give suggestions and guidelines for improvement, so that enterprises have more direction to improve and adjust and meet the information security requirements.

All our consultants have rich experience in information security, and have coached and audited many different organizations, so they can provide the best solutions close to the needs of our clients
The consultant team has performed all kinds of information security audits and has participated in business, education and entertainment, energy and other types of inspection operations, and can formulate customized information security inspection reports according to different needs
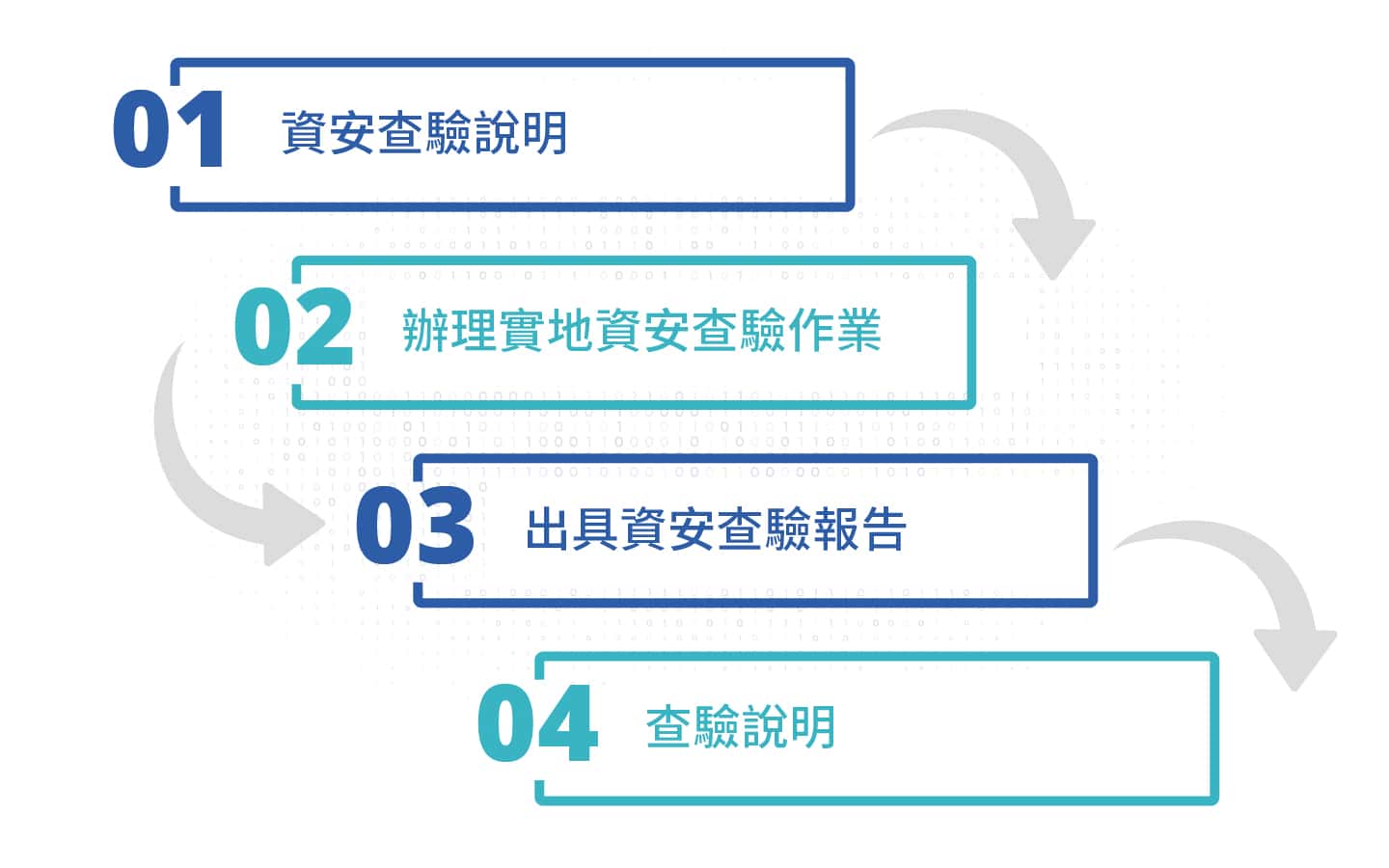
Before handling the inspection operation, our team will handle the explanation and inspection direction to facilitate the customer to prepare relevant information
The consultants can execute assessment operations according to the information security requirements of various grant programs, such as the Smart City and Township Living Application Grant Program, and assist clients in obtaining third-party fair certification